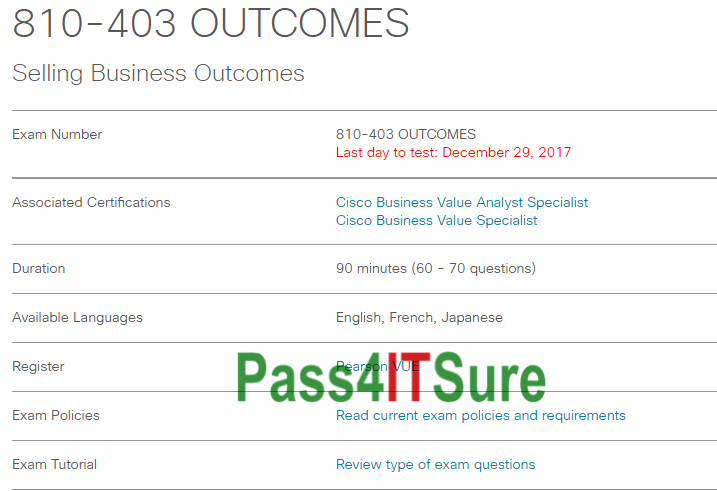
Can you pass the Cisco 810-403 dumps test by watching some videos? The Selling Business Outcomes (810-403 OUTCOMES) exam is a 90 minutes (60 – 70 questions) assessment in pass4itsure that is associated with the Cisco Business Value Analyst Specialist, Cisco Business Value Specialist certification. Pass the most important Cisco 810-403 dumps OUTCOMES exam questions video training with accurate answers. “Selling Business Outcomes” is the exam name of Pass4itsure Cisco 810-403 dumps test which designed to help candidates prepare for and pass the Cisco 810-403 exam. You will find them quite helpful and precise in the subject matter since all the exam content is regularly updated and has been checked for its accuracy. These easy to understand https://www.pass4itsure.com/810-403.html dumps questions and answers are available in downloadable PDF format to make it simpler to utilize, guaranteeing 100% success.
[Free New Pass4itsure 810-403 Dumps Version From Google Drive]: https://drive.google.com/open?id=0BwxjZr-ZDwwWZ0laMkIyTHdXeWM
[Free New Pass4itsure 642-883 Dumps Version From Google Drive]: https://drive.google.com/open?id=1cHxworTp2CNJ9BobLBGoggxUdcs3CmpZ
Free Pass4itsure 810-403 Dumps Exam Questions and Answers(1-28)
QUESTION 1
According to Cisco and related to customers, which is the one and only outstanding reason and justification for business outcome-based sales approach?
A. Executives are interested in satisfying customers’ needs and requirements.
B. Managers and supervisors are committed to close the quality of service gap.
C. Stakeholders are interested in being considered when developing and assessing business outcomes.
D. Customers are interested in solutions and services that result in measurable outcomes.
810-403 exam Correct Answer: D
QUESTION 2
RACI model aids can be used to understand specific aspects of stakeholders’ involvement in businesses. What does RACI stand for?
A. Responsible, Accountable, Consulted, Informed
B. Reconciler, Accountable, Consulted, Independent
C. Responsible, Assertive, Consulted, Informed
D. Reconciler, Assertive, Consulted, Informed
E. Responsible, Accountable, Consulted, Influenced
Correct Answer: A
QUESTION 3
Cisco solutions and services are related to every kind of outcomes. Which is the goal of business outcomes?
A. To enable CXOs or Line of Business leaders to grow revenues, lower operating costs and achieve strategic business objectives
B. To help customers establish new technology or evolve current functionality
C. To help customers operate, manage and optimize technology environment more effectively
D. To take advantage of new technology to increase business relevance
810-403 dumps Correct Answer: A
QUESTION 4
CSFs define what an organization should be good at. Which two options are characteristics of CSFs? (Choose two.)
A. CSFs are quantitative in nature and focus stakeholder relationships
B. CSFs describe an element that is needed by an organization or project to reach its goal
C. CSFs help link business initiatives or processes with selling, designing, developing, and adopting solutions and services
D. CSFs should receive special and continual attention from management in order to help the organization be effective
Correct Answer: BD
QUESTION 5
Which two options are part of customer relationship management? (Choose two.)
A. Developing market research.
B. Moving the customer towards positive decisions about IT investments and initiatives
C. Classifying customer segments.
D. Identifying key stakeholders.
810-403 pdf Correct Answer: BD
QUESTION 6
While troubleshooting a Sugar dashlet error in your web browser, you notice you are consistently receiving a 500 error in response to a particular REST API call. Which three actions would you perform to gain more insightinto the source of the problem?(Choose three.)
A. View the full list of browser cache contents.
B. View the Sugar log.
C. Visit status.sugarcrm.com to confirm there are no service outages.
D. Consult the Web server PHP error log.
E. Consult the JavaScript console in the Web browser.
Correct Answer: BDE
QUESTION 7
You are experiencing poor performance with your Sugar installation and want to install and configure Alternative PHP Cache (APC) and ensure it is enabled. Which two actions would help you achieve these goals? (Choose two.)
A. Install APC using the Sugar module loader and configure it from the Administration panel.
B. File a ticket with SugarCRM support requesting that APC be enabled for your instance.
C. Install the APC module from the PHP Extension Community Library (PECL) and configure it using the command line.
D. Verify the presence of the APC settings in the output of phpinfo().
810-403 vce Correct Answer: CD
QUESTION 8
You examine a Sugar database and discover some table names that end with the moniker ~_c~. What do the database tables with these names represent?
A. custom field data for custom fields
B. custom field metadata for custom fields
C. relationship data for custom relationships
D. relationship metadata for stock and custom relationships
Correct Answer: C
QUESTION 9
View the Exhibit.
A customization requires a developer to add a new profile action link to the MegaMenu shown in the exhibit. According to the Sugar Developer Guide, which directory should contain the customizations?
A. ~./custom/clients/base/views/profileactions/~
B. ~./custom/Extenslon/application/Ext/clients/base/views/profileactions/~
C. ~./custom/Extension/modules/Ext/clients/base/views/profileactions/~
D. ~./application/clients/base/views/profileactions/~
810-403 exam Correct Answer: B
QUESTION 10
According to the Sugar Developer Guide, which class should be used to store and retrieve system settings stored at the database level?
A. SugarAutoLoader
B. Administration
C. Configurator
D. SugarApplication
Correct Answer: C
QUESTION 11
You are attempting to load a large custom package using Module Loader andit is failing. Which three configuration values should you verify? (Choose three.)
A. PHP upload_max_filesize setting
B. Sugar import_max_records_total_limit setting
C. Sugar upload_maxsize setting
D. PHP memory_limit setting
E. PHP post_max_size setting
810-403 dumps Correct Answer: ADE
QUESTION 12
You need to execute a call to the Sugar REST v10API from within a customized controller. According to the Sugar Developer Guide, what would be the recommended method toaccomplish this task?
A. ~app.api.getRequest( )~
B. ~callback( )~
C. ~app.api.call( )~
D. ~$.ajax( )~
Correct Answer: C
QUESTION 13
You are working on the RecordView for a given module. You examine the data values contained in this.model and notice a discrepancy between those values and the list of fields contained in record.php. Which statement pertaining to this.model is correct?
A. Only values from stock fields listed in record.php are available.
B. Only values from any of the fields listed in record.php are available.
C. Only values from custom fields listed in record.php are available.
D. Only values from link fields listed in record.php are available.
810-403 pdf Correct Answer: B
QUESTION 14
You are creating an Initial one-to-one relationship from the Accounts module to a custom module using studio, which database schema change will occur?
A. Table accounts_cstm is created or modified.
B. Table [custom_module]_cstm is created or modified.
C. Table accounts is modified.
D. A new relate table is created.
Correct Answer: D
QUESTION 15
While troubleshooting a customization, you initiate a debugger session and examine the Sidecar metadata. Which two components would you expect it to contain? (Choose two.)
A. layouts
B. global variables
C. views
D. event handler
810-403 vce Correct Answer: AC
QUESTION 16
Which Sidecar component is nested within components of the same type?
A. field
B. layout
C. view
D. model
Correct Answer: B
QUESTION 17
In which two directories do Sidecar enabled modules read theirsubpanel layouts? (Choose two.)
A. ~./modules/[module]/metadata/subpanels/default.php~
B. ~./custom/modules/[module]/Ext/Layoutdefs/layoutdefs.ext.php~
C. ~./modules/[module]/clients/base/layouts/subpanels/subpanels.php~
D. ~./custom/modules/[module]/Ext/clients/base/layouts/subpanels/subpanels.ext.php~
810-403 exam Correct Answer: CD
QUESTION 18
Which Handlebars helper allows you to iterate over an array of objects?
A. models
B. for
C. foreach
D. each
Correct Answer: D
QUESTION 19 In the process of public key cryptography, which of the following is true?
A. Only the public key is used to encrypt and decrypt
B. Only the private key can encrypt and only the public key can decrypt
C. Only the public key can encrypt and only the private key can decrypt
D. The private key is used to encrypt and decrypt
E. If the public key encrypts, then only the private key can decrypt
810-403 dumps Answer: E
QUESTION 20. As per the guidelines in the ISO Security Policy standard, what is the purpose of the section on Physical and Environmental Security?
A. The objectives of this section are to avoid breaches of any criminal or civil law, statutory, regulatory or contractual obligations and of any security requirements, and to ensure compliance of systems with organizational security policies and standards.
B. The objectives of this section are to prevent unauthorized access, damage and interference to business premises and information; to prevent loss, damage or compromise of assets and interruption to business activities; to prevent compromise or theft of information and information processing facilities.
C. The objectives of this section are to provide management direction and support for information security.
D. The objectives of this section are to maintain appropriate protection of corporate assets and to ensure that information assets receive an appropriate level of protection.
E. The objectives of this section are to control access to information, to prevent unauthorized access to information systems, to ensure the protection of networked services, and to prevent unauthorized computer access.
Answer: B
QUESTION 21 During a one week investigation into the security of your network you work on identifying the information that is leaked to the Internet, either directly or indirectly. One thing you decide to evaluate is the information stored in the Whois lookup of your organizational website. Of the following, what pieces of information can be identified via this method?
A. Registrar
B. Mailing Address
C. Contact Name
D. Record Update
E. Network Addresses (Private)
810-403 pdf Answer: ABCD
QUESTION 22 You are aware of the significance and security risk that Social Engineering plays on your company. Of the following Scenarios, select those that, just as described, represent potentially dangerous Social Engineering:
A. A writer from a local college newspapers calls and speaks to a network administrator. On the call the writer requests an interview about the current trends in technology and offers to invite the administrator to speak at a seminar.
B. An anonymous caller calls and wishes to speak with the receptionist. On the call the caller asks the receptionist the normal business hours that the organization is open to the public.
C. An anonymous caller calls and wishes to speak with the purchaser of IT hardware and software. On the call the caller lists several new products that the purchaser may be interested in evaluating. The caller asks for a time to come and visit to demonstrate the new products.
D. An email, sent by the Vice President of Sales and Marketing, is received by the Help Desk asking to reset the password of the VP of Sales and Marketing.
E. An email is received by the Chief Security Officer (CSO) about a possible upgrade coming from the ISP to a different brand of router. The CSO is asked for the current network’s configuration data and the emailer discusses the method, plan, and expected dates for the rollover to the new equipment.
Answer: DE
QUESTION 23 During the review of the security logs you notice some unusual traffic. It seems that a user has connected to your Web site ten times in the last week, and each time has visited every single page on the site. You are concerned this may be leading up to some sort of attack. What is this user most likely getting ready to do?
A. Mirror the entire web site.
B. Download entire DNS entries.
C. Scan all ports on a web server.
D. Perform a Distributed Denial of Service attack through the Web server.
E. Allow users to log on to the Internet without an ISP.
810-403 vce Answer: A
QUESTION 24 What type of cipher is used by an algorithm that encrypts data one bit at a time?
A. 64-bit encryption Cipher
B. Block Cipher
C. Stream Cipher
D. Diffuse Cipher
E. Split Cipher
Answer: C
QUESTION 25 What encryption algorithm was selected to replace DES?
A. RC5
B. IDEA
C. AES
D. Blowfish
E. RSA
810-403 exam Answer: C
QUESTION 26 Which one of the following is an incorrect mod equation?
A. 9 mod 3 = 0
B. 40 mod 10 = 0
C. 40 mod 9 = 4
D. (6-1) mod 3 = 0
E. (2+4) mod 5 = 1
Answer: D
QUESTION 27 If you wish to change the permissions of a parent directory in your Linux system, and want the permissions to be changed on the files and subdirectories in the parent directory to be the same, what switch must you use?
A. -G
B. -R
C. -P
D. -S
E. -F
810-403 dumps Answer: B
QUESTION 28 You are working with some new RPM files on your Linux system. You know there are several options when dealing with RPM files. Which of the following answers lists proper RPM commands, with the correct description of the command?
A. rpm -q <package name> This command performs software verification.
B. rpm -e <package name> This command removes the software.
C. rpm -v <package name> This command performs software verification.
D. rpm -r <package name> This command removes the software.
E. rpm -i <package name> This command installs the software.
F. rpm -in <package name> This command installs the software.
Answer: ABE
These 810-403 dumps Selling Business Outcomes dumps are prepared by our experienced Cisco Specialists based on the recommended syllabus covering all the exam objectives. “Selling Business Outcomes”, also known as 810-403 exam, is a Cisco certification which covers all the knowledge points of the real Cisco exam. Pass4itsure Cisco 810-403 dumps exam questions answers are updated (166 Q&As) are verified by experts. The associated certifications of https://www.pass4itsure.com/810-403.html dumps is Cisco Business Value Analyst Specialist, Cisco Business Value Specialist.